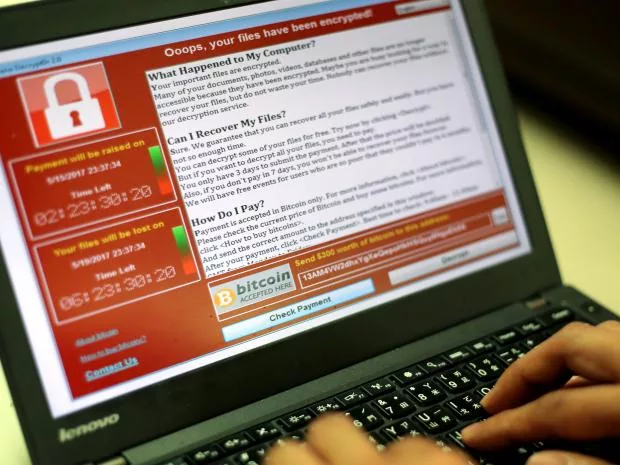
WannaCry Ransomware has caused so many problems in the last few weeks.
If your PC was one of those infected by the popular WannaCry ransomware that was released weeks ago, luck just hit you. The ransomware hit the web last Friday causing havoc to systems in over 180 countries around the world -the ransomware locked users files and requested for a $300 worth of bitcoin for those files to be unlocked.
This ransomware was a result of the hacking group “The Shadow Brokers”, who released tools it stole from NSA into the dark web. Those tools were now used by an unknown group of hackers to create the WannaCry ransomware and infect users running the Microsoft Windows.
Initially, a French security researcher called Adrien Guinet found a fix to the ransomware, a technique that could be used to get the secret encryption keys used by the hackers who created the WannaCry ransomware, but it works for only Windows XP compared to Windows XP, Windows 7, Windows Vista, Windows Server 2003 and 2008 operating systems that was stated at its release.
Adrien afterward released a WannaCry ransomware decryption tool, named WannaKey to his GitHub repo, in other to make it accessible to other security researchers who are willing to make an update that works across all windows operating system.
A security researcher named, Benjamin Delpy has made an upgrade to Adrien initial tool. He called it “WanaKiwi” and is compatible with Windows 7, Windows XP, Server 2003, Server 2008 and Vista.
Meanwhile for this new tool to work:
- You must not have rebooted your computer after it was infected.
- The associated memory has not been allocated and erased by some other process.
To use the WannaKiwi tool, download from Github and run command prompt. This new tool work on most affected Windows operating systems ranging from Windows XP, Windows 7, Windows Vista, Windows Server 2003 and 2008.
If you need a step-by-step procedure on how to use the tool, check out Matt Suiche from Comae Technologies here. He made a detailed explanation on how to use the tool.